Network security is vital for businesses and individuals in today’s digital world. IBM’s research reveals that global data breaches cost $4.45 million in 2023. This highlights the urgent need for strong cybersecurity strategies.
Cybersecurity is now essential for protecting sensitive information. Organisations face growing threats from clever cyber criminals. These attackers constantly develop new ways to exploit network weaknesses.
Data protection needs a thorough approach beyond basic security measures. Modern network security requires active monitoring and advanced technologies. It also demands a deep grasp of possible risks.
By using smart safeguards, businesses can lower their risk of cyber threats. This helps protect their most valuable digital assets. The changing digital landscape brings both challenges and opportunities.
Organisations must create flexible network security strategies. These should adapt to new tech environments and emerging threats. A complete approach combines tech solutions, staff training, and ongoing risk assessment.
Understanding Network Security Fundamentals
Protecting your computer network is crucial in today’s digital world. Cyber threats are growing more complex, demanding robust security measures. By 2020, experts predicted over 2 trillion gigabytes of data would exist.
Networks are vulnerable ecosystems that need constant vigilance. Most computer networks have weaknesses that can expose them to attacks. Recognising these threats is essential for building strong digital defences.
Types of Network Security Threats
Cyber attackers use various strategies to breach network security:
- Data theft
- Insider threats
- Malware attacks
- Password attacks
- Social engineering
Core Components of Network Protection
Effective network security combines multiple integrated security components:
- Multi-factor authentication – Requiring two separate identification methods
- Encryption protocols
- Firewall configurations
- Regular software updates
The Role of Network Architecture
Network architecture is the blueprint for security. Organisations can create subnetworks through strategic segmentation to limit potential breach impacts.
The CIA triad model (Confidentiality, Integrity, Availability) offers a framework for designing secure network infrastructures.
Network security is not a destination, but a continuous journey of adaptation and protection.
Essential Network Security Infrastructure
Protecting your digital ecosystem requires a robust approach to network security. Modern organisations must deploy comprehensive defence mechanisms against cyber threats. Network security strategies now demand intelligent and adaptive solutions.
A resilient network security framework involves multiple critical components. These work together to create an impenetrable digital fortress.
Firewall Implementation and Configuration
Firewall setup is the first line of defence in network protection. Organisations should implement multi-layered firewall strategies for optimal security.
- Stateful packet inspection
- Deep packet analysis
- Application-level filtering
- Intrusion prevention capabilities
Effective firewall configuration needs constant monitoring. Regular updates are crucial to address new security vulnerabilities.
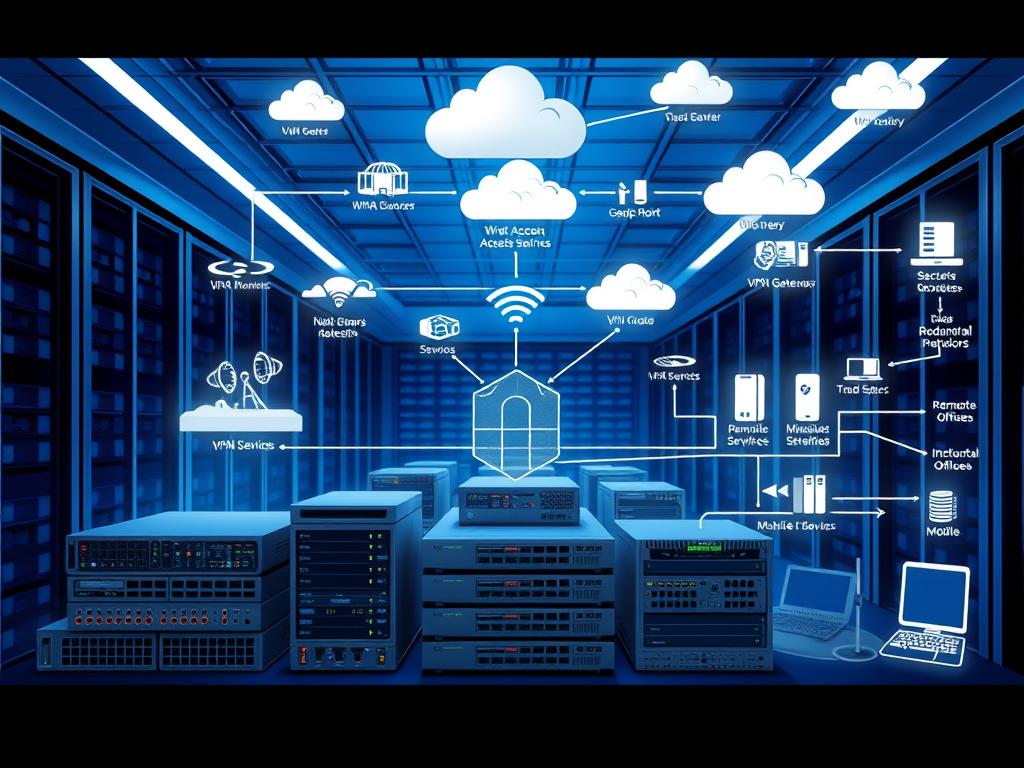
Virtual Private Networks (VPN) Configuration
VPN configuration is vital for secure remote work environments. Modern VPN solutions encrypt data packets to protect sensitive information during transmission.
Key considerations for VPN implementation include:
- Strong encryption protocols
- Multi-factor authentication
- Regular security assessments
Network Segmentation Strategies
Network segmentation splits corporate networks into smaller, manageable sections. This greatly reduces the impact of potential breaches.
Organisations can boost their security by using granular access controls. Isolating critical infrastructure also enhances overall security posture.
Effective network security is not about building walls, but creating intelligent, adaptive defence mechanisms.
How to Secure Computer Network
Protecting your computer network is vital in today’s digital world. Many organisations face cyber attacks yearly. Robust network security practices are now more important than ever.
To create a secure network, organisations need a comprehensive approach. This approach should address multiple security dimensions.
- Implement strong authentication methods
- Utilise advanced encryption techniques
- Conduct regular security assessments
- Develop comprehensive incident response plans
Critical network security strategies are essential. These include multi-factor authentication, zero trust network access, and network segmentation.
- Multi-Factor Authentication: Blocking 99.9% of automated attacks
- Zero Trust Network Access: Verifying every access request
- Network Segmentation: Limiting potential breach impacts
Key statistics show the importance of proactive security measures. These numbers highlight the need for strong cybersecurity strategies.
| Security Metric | Percentage |
|---|---|
| Organisations with cybersecurity strategy | 50% less likely to experience breaches |
| Data breaches caused by human error | 90% |
| Attacks targeting small businesses | 43% |
Embracing these network security best practices is crucial. Organisations can reduce their vulnerability to cyber threats. They can also protect their critical digital assets more effectively.
Data Encryption and Access Control
Protecting sensitive information is crucial for organisations worldwide. Data encryption acts as a vital shield against sophisticated digital threats. Cybersecurity experts recognise its importance in today’s digital landscape.

The statistics are alarming. 70% of organisations view data encryption as critical to their security strategy. Shockingly, 93% have faced a data breach in the past year.
These figures highlight the urgent need for robust security measures. Organisations must act swiftly to protect their valuable data.
Implementing Strong Encryption Protocols
Effective data encryption requires multiple layers of protection. Key strategies include whole disk encryption for portable devices. Encrypted email communications and secure transmission protocols are also essential.
- Whole disk encryption for portable devices
- Encrypted email communications
- Secure transmission protocols
“Encryption is not just a technology, it’s a fundamental defence mechanism in the digital world.” – Cybersecurity Expert
Access Management Best Practices
Access control is crucial for network security. Organisations must implement stringent permission management to prevent unauthorised data access. This helps safeguard sensitive information from potential threats.
- Implement role-based access controls
- Regularly audit user permissions
- Use principle of least privilege
Multi-factor Authentication Systems
Multi-factor authentication adds an extra security layer beyond passwords. It requires multiple verification methods to access systems. This significantly reduces the risk of unauthorised access to sensitive data.
80% of enterprises use Virtual Private Networks for secure communications. 90% plan to increase their investments in encryption technology. These trends show that comprehensive data protection is now essential.
Employee Training and Security Awareness
Employees are crucial in cybersecurity defence. They can be both a strong shield and a potential weakness. A staggering 95% of cybersecurity issues stem from human error.
In 2023, 70% of data breaches involved human elements. This highlights the urgent need for robust employee education programmes. Comprehensive security awareness training is essential for organisations.
Employee training evolves beyond traditional methods. Regular security sessions can turn staff into proactive cyber defenders. The Federal Virtual Training Environment offers a 6-hour course.
FEMA provides a one-hour workplace security awareness programme. These accessible learning pathways use interactive modules and real-world scenarios. Such approaches can greatly improve an organisation’s incident response capabilities.
Developing strategic security policies is crucial. It helps create a culture of vigilance within the organisation. Training programmes should address specific risks, especially for remote and hybrid workers.
Over 33% of the workforce now operates remotely or in hybrid models. Regular phishing simulations and practical workshops can boost detection rates. These measures also reduce potential breach risks.
Investing in security awareness training is cost-effective. The average global data breach cost $4.45 million in 2023. Proactive employee education is a powerful defence mechanism.
Empowering staff with knowledge and tools is vital. It transforms the workforce into a resilient, security-conscious network. This approach actively protects an organisation’s digital assets.
FAQ
What are the most common network security threats?
Network security threats include malware, phishing attacks, and ransomware. Denial of service attacks and insider threats also pose risks. These can compromise data, disrupt operations, and cause financial damage.
How often should we update our network security infrastructure?
Review and update network security infrastructure quarterly. Regular assessments help identify vulnerabilities and implement the latest security patches. This ensures your defences remain robust against evolving cyber threats.
What is network segmentation and why is it important?
Network segmentation divides a computer network into smaller, isolated subsections. It limits potential breach impacts and controls access between different network zones. This approach significantly reduces the risk of widespread cyber attacks.
How effective are Virtual Private Networks (VPNs) in protecting network security?
VPNs are crucial for securing remote connections by encrypting data transmission. They mask IP addresses and create secure tunnels between devices and networks. VPNs provide essential protection for organisations with distributed or remote workforces.
What is multi-factor authentication, and why should we implement it?
Multi-factor authentication (MFA) requires users to provide two or more verification factors for network access. It adds extra security layers beyond traditional password protection. MFA significantly reduces the risk of unauthorised access.
How can employees contribute to network security?
Employees play a critical role by maintaining security awareness and following established protocols. They should recognise potential phishing attempts and use strong passwords. Reporting suspicious activities promptly is crucial.
Regular training programmes are essential in developing a security-conscious workforce.
What encryption protocols are most recommended for businesses?
Advanced encryption standards like AES-256, TLS 1.3, and SSL/TLS protocols are recommended. These provide strong encryption mechanisms for robust data protection. They safeguard sensitive information during transmission and storage.
How quickly should an organisation respond to a potential security breach?
Immediate response is crucial. Organisations should have pre-established incident response procedures. These enable swift identification, containment, and mitigation of potential security breaches.
Typically, action should be taken within 4-6 hours of detection.
What are the key components of a comprehensive network security strategy?
A robust strategy includes firewalls, intrusion detection systems, and encryption. Access control, regular security audits, and employee training are also crucial. Incident response planning helps create a comprehensive defence mechanism.
How can small businesses improve their network security with limited resources?
Small businesses can use cloud-based security services and open-source security tools. Implementing multi-factor authentication and regular staff training is essential. Basic security practices like strong password policies and routine software updates are cost-effective solutions.