Your network security key is vital for internet safety and connectivity. It’s your Wi-Fi password, guarding against unauthorised access to your wireless network. This digital shield protects your personal information from prying eyes.
A network security key is typically 8-12 characters long. It mixes letters, numbers, and special symbols. This unique code forms a strong barrier against cyber threats.
Finding and managing your Wi-Fi password is crucial for digital security. This skill is useful for both tech novices and experts alike.
Our guide will show you how to locate your network key. We’ll cover different devices and platforms for your convenience.
Understanding network key management gives you more control over your internet access. It also helps protect your digital world from security risks. Let’s explore network security keys and boost your online experience.
Understanding Network Security Keys and Their Importance
Network security keys are vital guardians of our online privacy and data protection. These digital credentials act as the first defence against cyber threats. They ensure only authorised users can access wireless networks.
Network security uses multiple encryption protocols to safeguard digital communications. These protocols have evolved remarkably over time. They’ve progressed from early WEP to the cutting-edge WPA3 standard.
What Defines a Network Security Key?
A network security key is a unique passcode that blocks unauthorised access to wireless networks. Cybersecurity experts suggest creating strong keys.
- 12-16 characters long
- Composed of uppercase and lowercase letters
- Including numbers and special characters
- Avoiding easily guessable words
Evolution of Encryption Protocols
Wireless encryption protocols have shown significant security improvements over time. Each new protocol offers better protection than the last.
| Protocol | Security Level | Key Characteristics |
|---|---|---|
| WEP | Low | Vulnerable, easily compromised |
| WPA | Medium | Improved encryption |
| WPA2 | High | Advanced Encryption Standard (AES) |
| WPA3 | Very High | Strongest protection against attacks |
Protecting Your Digital Privacy
The U.S. Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) highlights the importance of network security keys. These keys help prevent various online threats.
- Piggybacking
- Wardriving
- Evil twin attacks
- Wireless sniffing
- Unauthorized computer access
Remember: A strong network security key is your first defence against potential cyber intrusions.
Common Terms for Network Security Keys Across Different Platforms

Wireless network security can seem like a complex language. Network security keys have various names across platforms and devices. Understanding these terms helps you manage your Wi-Fi key confidently.
Here are the most common names for network security keys:
- Wireless password
- Network password
- Wi-Fi key
- WEP/WPA key
- Network security key
These terms all serve the same purpose: protecting your wireless network. Different manufacturers and providers may use slightly different names. This can sometimes puzzle users.
Encryption protocols also influence how these keys are named:
- WEP: Supports up to 232-bit encryption keys
- WPA: Supports encryption up to 256 bits
- WPA2: Offers two modes – Personal (home) and Enterprise (business)
- WPA3: The newest protocol with enhanced security features
Experts suggest changing your network security key every 6 to 12 months. When creating a new key, use a mix of characters. Include uppercase and lowercase letters, numbers, and special symbols.
Remember: A strong network security key is your first line of defence against potential cyber intrusions.
How to Find Network Security Key on Computer
Finding network security keys needn’t be a headache. This guide will help you unlock the secrets of wireless connectivity. You’ll learn how to access Wi-Fi passwords for your devices.
Knowing how to find your network security key is vital. Most Windows users rely on built-in interfaces. Mac users often use Keychain Access. These methods can save you time and bother.
Discovering Your Network Key on Windows 10/11
Windows makes viewing network security key info easy. Here’s how to see your network security key settings:
- Open Network & Internet settings
- Click on Wi-Fi option
- Select your connected network
- Choose Network properties
- Click Show password
Locating Network Key on macOS
Mac users can fetch their Wi-Fi password through Keychain Access. This method is popular among many macOS users. Here’s how:
- Open Spotlight Search
- Type “Keychain Access”
- Search for your network name
- Double-click the network
- Check “Show password”
Accessing Network Key Through Router Settings
Most routers offer a direct way to view network security key info. Check your router’s admin panel by entering its IP address in a browser. You’ll usually need the admin username and password for access.
Pro tip: Keep your network security key private. Change it often for better security.
Different Types of Network Encryption Protocols
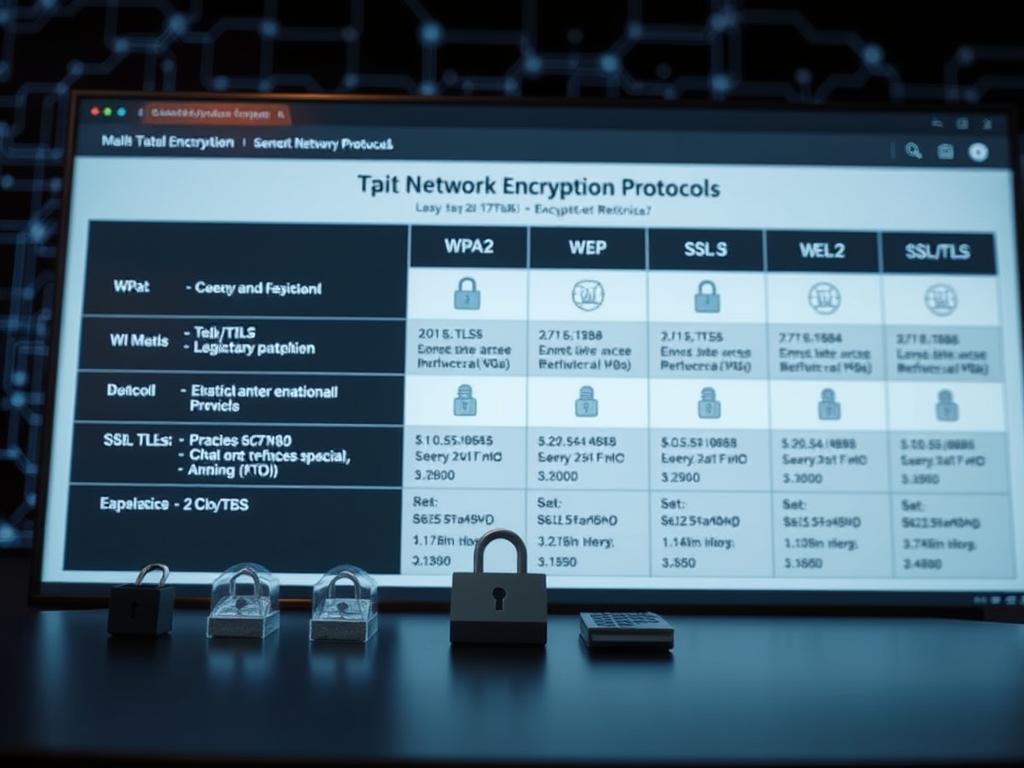
Network security has changed a lot since the early days of the internet. Knowing about encryption standards is vital for protecting digital chats and privacy online.
The story of network encryption shows how security tech has grown over time. Let’s explore the key protocols that have shaped online safety.
- WEP (Wireless Equivalent Privacy): The first wireless encryption protocol, now considered completely obsolete
- WPA (Wi-Fi Protected Access): Introduced significant improvements over WEP
- WPA2: Implemented Advanced Encryption Standard (AES), providing robust security
- WPA3: The latest and most secure encryption protocol
WEP encryption was very weak. Hackers could easily break into networks using this old method.
As online threats got smarter, network security needed big upgrades. WPA2 became the new standard for WiFi devices.
It uses complex maths to make networks much safer. This makes it really hard for hackers to get in.
WPA3 is the best network encryption we have now. It gives each user their own data encryption.
This makes it much harder to guess passwords offline. WPA3 keeps you safe on both public and private networks.
The evolution of network encryption demonstrates humanity’s ongoing commitment to digital security and privacy protection.
New encryption standards keep getting better. They make sure our online chats stay private and safe in our connected world.
Troubleshooting Network Security Key Mismatch Errors
Network security key mismatch errors can make wireless connectivity a real headache. These digital roadblocks affect about 30% of wireless connection attempts. They turn simple internet access into a tricky task.
Common Causes of Network Key Mismatches
To fix Wi-Fi connection problems, you need to know what causes them. Several factors can lead to network security key mismatch errors.
These include corrupt network drivers, which affect 25% of users. Third-party antivirus software can also cause issues in 15% of cases. Outdated router settings and wrong passwords are other common culprits.
Practical Steps to Resolve Connection Issues
To fix network key mismatch errors, you need a step-by-step approach. Here are some proven ways to get your wireless connection back on track:
- Restart the router – Resolves connectivity issues in 40% of cases
- Forget and reconnect to the wireless network
- Update network drivers
- Temporarily disable antivirus software
- Refresh IP settings using command line
“Patience and methodical troubleshooting are your best allies in resolving network connectivity challenges.”
When to Seek Technical Support
Sometimes, basic fixes won’t solve your network key mismatch. In these cases, you might need expert help. Consider getting professional support if:
- Multiple troubleshooting attempts have been unsuccessful
- You suspect hardware-related issues
- Complex network configurations are involved
Most of the time, you can fix connectivity issues on your own. About 70% of problems can be solved through basic troubleshooting. This means you can handle most network security key challenges by yourself.
Best Practices for Managing Network Security Keys
Safeguarding your digital world requires smart network security key management. Strong passwords are vital. They form the first defence against cyber attacks.
Boost your network’s protection with effective password strategies. Here are key practices to consider:
- Create complex passwords with at least 12 characters
- Combine uppercase and lowercase letters, numbers, and symbols
- Avoid using personal information in your passwords
- Use unique passwords for different networks
Updating your network security key regularly is crucial. Experts suggest changing passwords every three to six months. This helps prevent unauthorised access and reduces long-term risks.
| Security Practice | Recommended Action |
|---|---|
| Password Length | Minimum 12 characters |
| Password Complexity | Mix of letters, numbers, symbols |
| Update Frequency | Every 3-6 months |
Password management tools can make your life easier. They help create unique, complex passwords. These tools also reduce the risk of reusing passwords across networks.
Adopt these best practices to protect your digital assets. You’ll develop a proactive approach to network security. This will help shield you from potential cyber threats.
Conclusion
Network security keys are vital for digital protection. By grasping online privacy, you can safeguard your digital world effectively. This knowledge helps create a strong defence against cyber threats.
WPA2 and WPA3 offer advanced protection for wireless networks. Regular key updates reduce the risk of unauthorised access. A strong key mixes uppercase, lowercase letters, numbers, and special characters.
Staying informed about digital protection is crucial as technology evolves. Each security step protects your personal information. Be vigilant about online privacy to secure your digital space.
The digital landscape is complex, but you can navigate it confidently. Your commitment to network security protects your devices. It also contributes to a safer online environment for everyone.